NEW! Space systems security engineering professional certification program...by parallax cyber academy
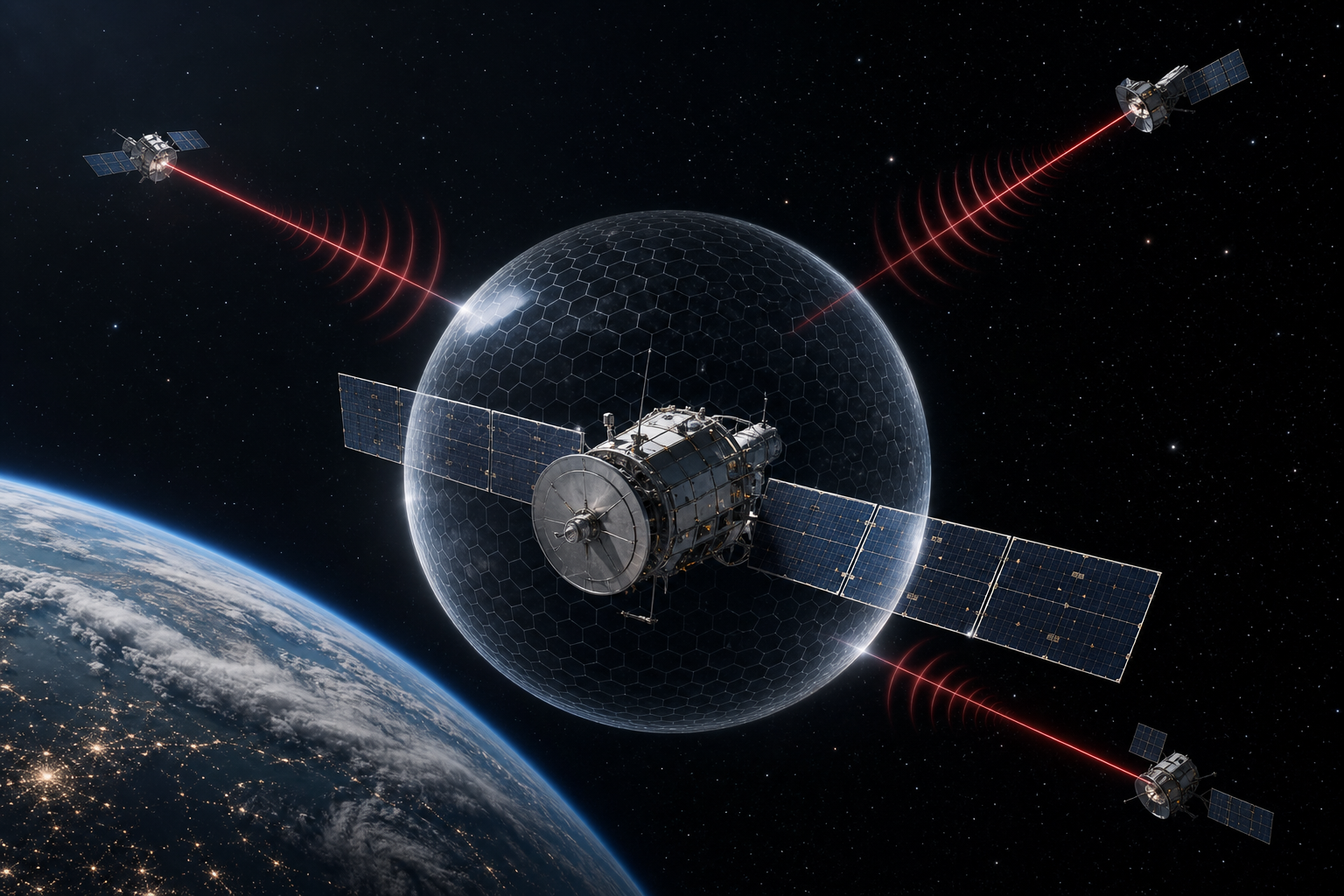
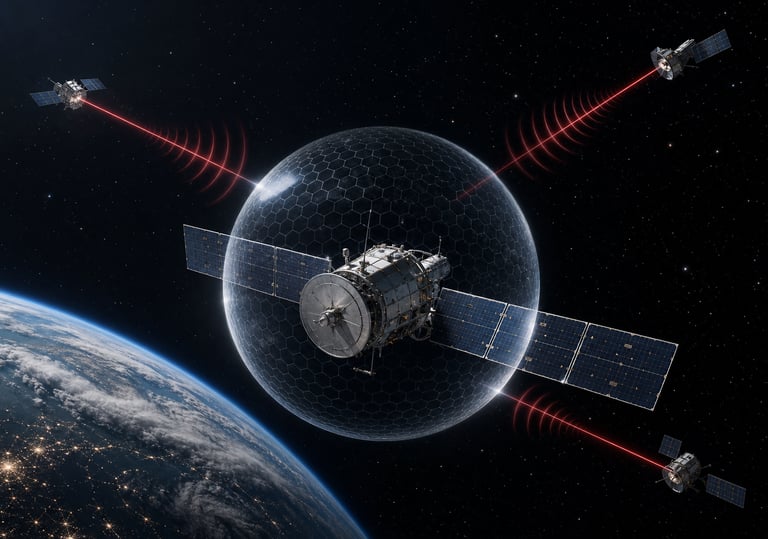
Defending and Attacking Space Systems in Cyberspace
A Systems Security Engineering Analysis
Course SC201
New availability: 8 July 2026 (1 Day)
Course Overview
SC201 advances from foundational awareness to practitioner capability--competencies that actually defend space systems and expose adversary techniques. It takes a deliberate two-sided view: teaching how to build and validate strong defenses across all four space system segments, and how adversaries plan and execute offensive cyber operations against those same systems. Participants leave with practical grounding in engineering-lifecycle vulnerability management, Defensive Cyber Operations (DCO), SPARTA-based threat emulation, cybersecurity policy compliance, and the testing frameworks that connect adversarial findings to authorization decisions.
What You'll Learn
Eight lessons move from engineering vulnerability management to strategic counter-space operations:
Engineering security into the Systems Development Life Cycle (SDLC): DevSecOps practices adapted for hardware-intensive space programs, including threat modeling at design reviews and security gate integration in CI/CD pipelines
Software Bill of Materials (SBOM) and Hardware Bill of Materials (HBOM) management: generating and governing bills of materials as active security tools, with NVD and CVE integration for vulnerability prioritization in constrained on-orbit patching environments
DCO principles: configuration management, runtime exposure monitoring using telemetry and SIEM, threat detection via indicators of compromise, and incident response playbooks calibrated for space operations
Cybersecurity frameworks at intermediate depth: NIST SP 800-53 control families mapped to DCO activities, NISPOM compliance for cleared facilities and personnel, and ITAR obligations that directly affect DevSecOps workflows and software repository access
Segment-specific DCO: zero-trust ground networks, on-orbit command authentication and software integrity verification, anti-jamming and anti-spoofing for the link segment, and user endpoint protection
Cyber threat emulation: SPARTA TTPs, hardware-in-the-loop testbeds, digital twin environments, software-defined radio injection tools, and structured red/blue team exercises for space operations personnel
Testing frameworks: Verification and Validation, Cyber Resiliency T&E, and Operational T&E — mapped to SDLC phases and tied to RMF authorization evidence requirements
Counter-space cyber operations: targeting cycle principles, proportionality and collateral effect assessment, international law and the Outer Space Treaty, and deterrence theory for the space domain
How Space Cybersecurity Differs from Enterprise Cybersecurity
Operational Technology for Spacecraft
Testing satellite security requires hardware-in-the-loop testbeds, software emulators, and digital twin environments, because the target system cannot be fully replicated in a laboratory with the fidelity that enterprise penetration testing takes for granted. The SPARTA framework taught in SC201 catalogues space-domain TTPs with no enterprise analogue, including orbital mechanics manipulation via navigation spoofing and on-orbit payload mode switching, giving practitioners a vocabulary that is native to the space threat environment rather than borrowed from enterprise or ICS frameworks.
Special Mission Data Handling for Ground Systems
Space program BOM management must simultaneously satisfy NIST vulnerability management, ITAR country-of-origin tracking, and NISPOM supply chain security—all three frameworks at once. An enterprise SBOM tracks dependencies on a quarterly patch cycle; a space program SBOM must account for software running, potentially without updates, for 15 years and for the regulatory implications of every component's origin and handling classification. SC201 teaches participants to treat BOM governance as a unified compliance activity, not three separate reporting burdens.
Long-Range Communications and the Link Segment
Link segment DCO has no enterprise parallel. Adversaries can attack satellite communications without ever touching a network—using only radio hardware to jam, spoof, or inject signals through open electromagnetic spectrum. SC201 teaches techniques including anti-jamming, signal authentication methods, and link encryption standards alongside the operational trade-offs between security measures and the bandwidth and power budgets that constrain every space mission. These are engineering decisions made at design time (a.k.a. Security by Design), years before the threat landscape is fully known, making the conceptual grounding SC201 provides directly applicable to program work.
NOTE: This course is often available as part of a course package, where each course is taught in a series. When registering, watch for combined courses availability.